Introduction
The Critical Role of SPF, DKIM, and DMARC in Email Security
Ever received a sketchy email?
You're not alone.
SPF, DKIM, and DMARC are your safeguards in the wild world of email.
SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) work hand-in-hand to validate the origin of email messages. They ensure the email you think is coming from your bank.
DMARC (Domain-based Message Authentication, Reporting & Conformance) takes it a step further by specifying what should happen if an email fails these checks.
Why should you care?
According to data from the FBI’s Internet Crime Complaint Center, phishing scams cost Americans $57 million in 2019 alone.
That's a lot of cheddar, my friend.
Decoding Email Authentication: A Primer
Unpacking SPF: The Sender Policy Framework
Ever wonder how your email provider knows what's spam and what's not?
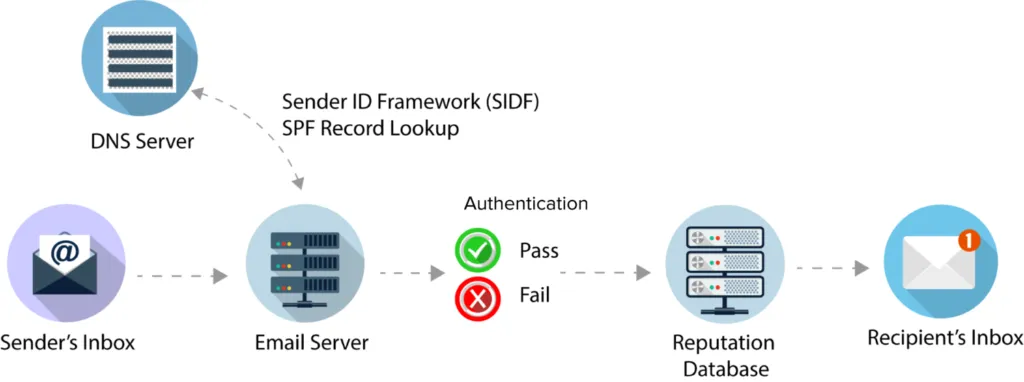
Enter SPF or Sender Policy Framework.
It's a protocol that helps your email server figure out if an incoming email is from a trusted source.
Think of it as a bouncer at a club, only letting in the VIPs—your legitimate emails. SPF uses DNS records to validate the sending mail server, ensuring it's on your own domain host's approved list.
Demystifying DKIM: DomainKeys Identified Mail
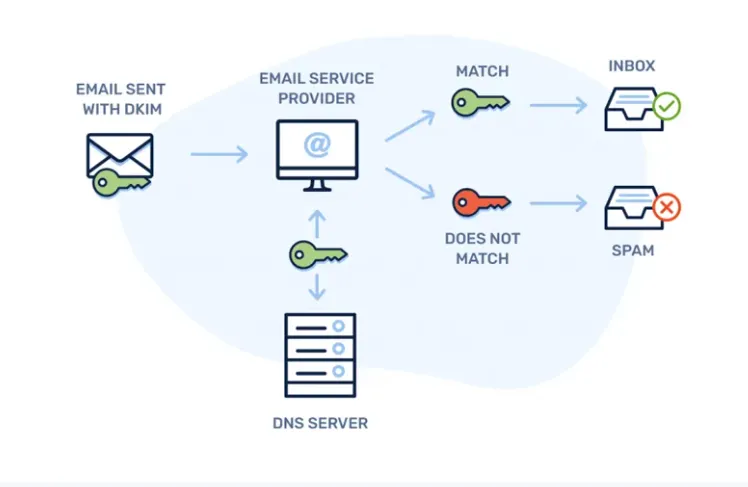
It adds an encrypted signature to your emails, making it nearly impossible for scammers to tamper with them.
When an email arrives, the receiving server uses the public key stored in your domain's DNS records to decrypt the DKIM signature. If it matches, you're in the clear!
Understanding DMARC: Domain-based Message Authentication, Reporting & Conformance

Last but not least, DMARC.
It's the team leader who ensures that both SPF and DKIM are doing their jobs correctly.
If an email fails either of these checks, DMARC dictates what happens next—whether it's sent to the spam folder or rejected outright. It's your final line of defense in email security.
SPF: More Than Just Sun Protection for Your Domain
The Inner Workings of SPF
Ever wondered why some emails land directly in your inbox while others get shunted to the spam folder?
No, it's not magic; it's SPF or Sender Policy Framework.
This protocol helps email servers distinguish between genuine emails and potential spam.
SPF verifies the sending mail server's IP addresses against a list of authorized IP addresses in your domain's DNS records.
When an email passes this SPF authentication, it's more likely to reach the recipient's inbox rather than their spam folder.
So, neglecting SPF is like leaving your front door open if you're a domain owner.
Real-world Scenarios: The Consequences of Ignoring SPF
Let's get real for a moment. Imagine you're a small business domain owner, and you've just launched a new product.
You're excited to email your customer base, but you've ignored setting up an SPF record in your domain's DNS settings.
What happens?
Your email might be treated as unauthenticated mail, landing in spam folders instead of email inboxes. Now, your big launch turns into a big flop.
On the flip side, if you're a consumer, an email without SPF could be a phishing attack waiting to happen. Either way, the stakes are high.
Essential Apps to Include in Your SPF Record
If you're using third-party email service providers like Google Workspace for sending emails, you'll need to include them in your SPF record.
This ensures that emails sent through these platforms are authenticated, boosting your email deliverability rates.
DKIM: The Digital Handshake in Email Communication
The Technicalities of How DKIM Functions
Ever wondered how email servers know emails are coming from the real domain name owner and not being spoofed?
Well, with the help of DKIM, or DomainKeys Identified Mail.
It's like a secret handshake for your emails.
When you send an email, your mail server attaches a unique DKIM signature and return address.
This digital signature is a string of characters generated based on the email header and content and a private key only known to your domain.
It's a crucial part of email authentication methods that help reduce spam and ensure your emails reach the recipient's inbox, not their spam folder.
Digital Signatures: The Backbone of DKIM
The receiving mail server uses your domain's public key, stored in your domain's DNS records, to validate the DKIM signature.
It's like a secret handshake confirming you're legit if it matches.
This is where the domain owner's responsibility kicks in.
You need to ensure your DNS records, especially the DKIM records, are set up correctly.
Incorrect DNS settings could lead to email delivery issues, affecting your email deliverability rates.
How DKIM Influences Your Email's Journey to the Inbox
Without DKIM authentication, your emails could be mistaken for phishing attacks or spam, ending up in the dreaded spam folder. And let's face it, no one checks their spam folder regularly.
DKIM authenticates your outgoing messages and influences how email service providers perceive your domain.
DMARC: The Watchtower of Your Email Ecosystem
The Compelling Reasons to Implement DMARC
Imagine your email system as a bustling city.
DMARC acts as the watchtower, keeping an eye on every email message that comes and goes.
Why should you care?
Because DMARC, when combined with SPF and DKIM, forms an impenetrable line of defense against email spoofing and phishing attacks.
In short, DMARC improves your email deliverability and protects your domain's reputation.
The Synergy Between DMARC, SPF, and DKIM
Think of DMARC as an orchestra conductor, with SPF and DKIM as the musicians.
SPF verifies the IP addresses sending mail on behalf of your domain, while DKIM adds a layer of authentication through a digital signature.
DMARC takes these two methods and adds a set of policies that dictate how to handle emails that fail these checks.
It's a harmonious relationship that ensures your emails reach the inbox and are free from tampering.
Navigating DMARC Policies and Reporting Metrics
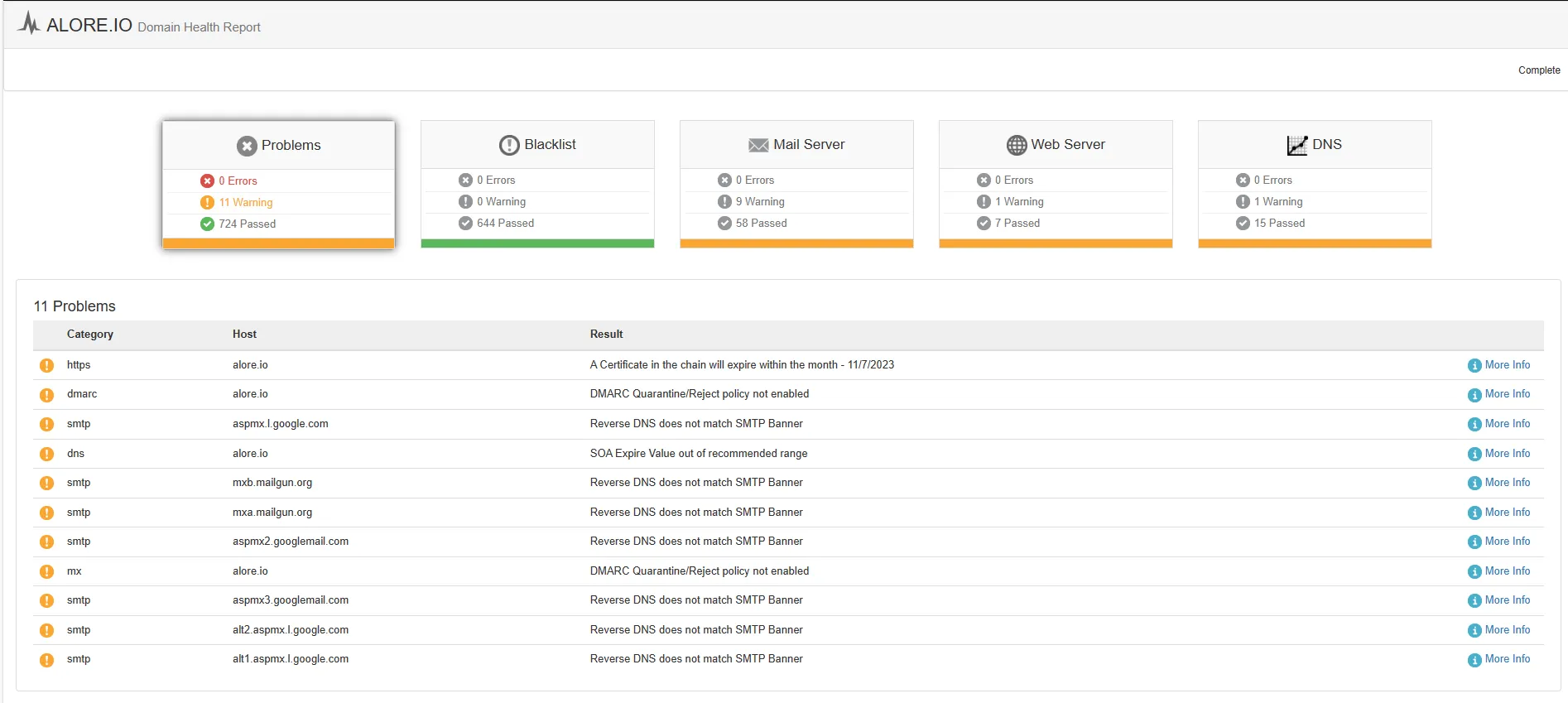
Setting up DMARC might seem like a daunting task, but it's easier than you think.
Your first step is to navigate to your domain's DNS settings and add a DMARC record.
This record outlines your policies for how receiving servers should handle unauthenticated messages.
But DMARC doesn't stop there; it also provides invaluable reporting metrics.
These metrics give domain owners insights into who is sending emails on their behalf, making identifying legitimate and malicious activity easier.
The Harmonious Trio: SPF, DKIM, and DMARC in Concert
The Interconnected Mechanics of SPF, DKIM, and DMARC
You're here because you want your emails to reach the recipient's inbox and be trusted. That's where SPF, DKIM, and DMARC come into play.
These three authentication methods are like the Three Musketeers of email security.
SPF (Sender Policy Framework) is your first line of defense, verifying the IP addresses from which emails are sent.
DKIM (DomainKeys Identified Mail) adds a digital signature to your outgoing messages, ensuring they haven't been tampered with.
Finally, DMARC (Domain-based Message Authentication, Reporting & Conformance) sets the rules, telling email servers how to handle unauthenticated mail. When these three work in concert, your email deliverability sings.
Your DIY Guide to Email Authentication Setup
SPF: Crafting Your DNS TXT Records
You'll need to access your domain's DNS settings to set up your SPF. Once there, add a TXT record that outlines which mail servers are authorized to send emails on behalf of your domain. This is crucial for email deliverability.
DKIM: Setting Up Domain's DNS Settings and Digital Signatures
This is another layer of authentication that uses digital signatures to verify that an email message wasn't altered in transit.
To implement DKIM, you'll need to add another TXT record in your domain's DNS settings.
This record will contain your public and private keys, both of which receiving mail servers use to decode the email's digital signature. If the signature matches, your email gains another level of trust.
Did You Know? DKIM also helps in protecting against phishing attacks, adding an extra layer of email security.
DMARC: Policy Configuration and Report Analysis
Last but not least, let's delve into DMARC (Domain-based Message Authentication, Reporting, and Conformance).
This is the watchtower that uses SPF and DKIM records to decide an email's fate. To set up DMARC, you'll need to add a DMARC record to your domain's DNS settings. This record outlines what should happen to emails that fail SPF or DKIM checks.
DMARC also provides reporting metrics, helping domain owners understand how their email is performing. These reports can be a goldmine of information, offering insights into email deliverability and security.
Action Item: Don't ignore DMARC reports. They can offer valuable insights into authentication methods and even flag potential domain spoofing attempts.
Pro Tips
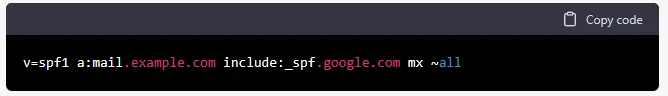
Understanding the syntax of an SPF record
An SPF (Sender Policy Framework) record is a type of DNS record that helps to protect against email spam and phishing attacks.
- It specifies which mail servers are authorized to send emails for a specific domain.
- The syntax for an SPF record includes a number of different elements:
- The version of SPF that is being used (e.g. v=spf1).
- A list of mechanisms defining which servers can send emails for the domain (e.g. a, mx, include).
- A list of domain names or IP addresses that correspond to the allowed servers.
- A "mechanism" that specifies what to do if the email is not from an authorized server (e.g. ~all, -all, ?all).
An example of an SPF record syntax might look like this:
v=spf1 a mx include:_spf.google.com -all
- This means that the SPF record is using version 1, allowing the domain's A and MX servers to send emails and any servers included in the Google Apps SPF record. If the email is not from one of these authorized servers, it should be treated as a failed SPF check (-all).

Common Errors in SPF Records
Here are a few common errors that can occur when setting up an SPF record:
- Too many DNS lookups: An SPF record should not contain more than 10 DNS lookups, as it can cause delays in email delivery.
- Incorrect syntax: An SPF record must follow a specific syntax, and any mistakes in this syntax can cause the record to be ignored by email servers.
- Incorrect IP addresses: If an SPF record lists the wrong IP addresses for an email server, it may prevent emails from being delivered.
- Missing or incorrect include statements: If an SPF record is missing an include statement for an external email service that is being used, or if the include statement is incorrect, it may prevent emails from being delivered.
- Incorrect mechanism: If an SPF record uses the wrong mechanism (e.g., all instead of ~all), it may cause legitimate emails to be treated as spam.
- Multiple SPF records: A domain with multiple SPF records can cause confusion and prevent emails from being delivered. There should only be one SPF record per domain.



Understanding the syntax of a DMARC record
A DMARC record is a DNS (Domain Name System) record that specifies a domain's DMARC policy and any other relevant details. Here is the syntax for a DMARC record:
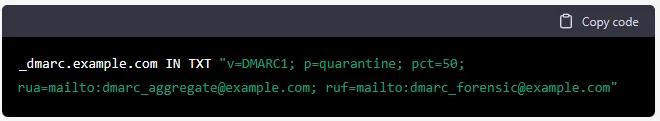
In this example, _dmarc.example.com is the subdomain where the DMARC record is located, IN indicates that this is an Internet record, and TXT indicates that the record is a text string.
The text string itself is a series of key-value pairs separated by semicolons. The keys and values in this example are as follows:
- v=DMARC1: This specifies the version of DMARC being used.
- p=quarantine: This specifies the DMARC policy. In this case, the policy is set to "quarantine", which means that emails that fail DMARC checks should be quarantined (i.e. moved to a separate folder or labeled as suspicious) rather than rejected.
- pct=50: This specifies the percentage of emails that should be subject to the DMARC policy. In this case, 50% of emails that fail DMARC checks will be quarantined.
- rua=mailto:dmarc_aggregate@example.com: This specifies the email address where DMARC aggregate reports should be sent.
- ruf=mailto:dmarc_forensic@example.com: This specifies the email address where DMARC forensic reports should be sent.
Common Errors in DMARC Records
Here are some common errors that can occur in DMARC records:
- Missing or incorrect "v" key: The "v" key specifies the version of DMARC being used. If this key is missing or incorrect, email receivers may not be able to interpret the DMARC record correctly.
- Missing or incorrect "p" key: The "p" key specifies the DMARC policy, which determines how email receivers should handle emails that fail DMARC checks. Email receivers may not know how to handle emails that fail DMARC checks if this key is missing or incorrect.
- Incorrect "pct" value: The "pct" key specifies the percentage of emails that should be subject to the DMARC policy. If the value for this key is not a valid integer between 0 and 100, email receivers may not be able to interpret the DMARC record correctly.
- Missing or incorrect "rua" or "ruf" key: The "rua" and "ruf" keys specify the email addresses where DMARC aggregate and forensic reports should be sent, respectively. If these keys are missing or the email addresses are invalid, DMARC reports may not be delivered to the correct recipients.
- Incorrect syntax: DMARC records are DNS records that follow a specific syntax. If the syntax of the DMARC record is incorrect, email receivers may not be able to interpret the record correctly.
FAQs: Quick Solutions to Your Burning Questions
What are DNS TXT records?
DNS TXT records are used to hold text information for a domain.
In the context of email authentication, they store data for SPF, DKIM, and DMARC. You'll need to consult your DNS provider to set these up.
How can I improve email deliverability?
Improving email deliverability involves multiple factors, including but not limited to setting up SPF, DKIM, and DMARC. These authentication methods help ensure that your email messages are not marked as spam, thereby increasing the chances of them landing in the recipient's inbox.
What is email spoofing?
Email spoofing is when an attacker sends emails that appear to come from a domain other than the one they actually originated from. This is where SPF and DKIM come into play; they authenticate the domain owner and the email sender, making it difficult for spoofers to succeed.
What happens if I don't authenticate email?
If you don't use email authentication methods like SPF, DKIM, and DMARC, your email messages are more likely to be flagged as spam or not delivered at all. This can severely impact your email deliverability and could even lead to your domain being blacklisted.
What are phishing attacks, and how can I prevent them?
Phishing attacks are fraudulent attempts to obtain sensitive information by disguising it as a trustworthy entity. Implementing SPF, DKIM, and DMARC can significantly reduce the risk of phishing attacks targeting your domain.
How can I receive messages about my DMARC policy?
DMARC policies include reporting metrics that can be sent to a specified email address. These reports provide valuable insights into your email authentication performance, helping you fine-tune your settings for optimal deliverability.
What is the role of the domain provider and DNS provider in email security?
Your domain provider is where you've registered your domain name, and your DNS provider hosts the DNS records for that domain.
Both play crucial roles in email security, as you'll need to access these platforms to set up SPF, DKIM, and DMARC records.
What Should I Know About DNS System and DNS Servers?
The DNS system is the phonebook of the internet, translating human-friendly domain names into IP addresses.
DNS servers are the databases that hold this information. They play a crucial role in email delivery and security.
What's the Role of a Private Key in DKIM?
A private key is used to create the DKIM signature for outgoing messages from your mail server.
It's crucial to keep this key secure, as it's used to validate your email messages on the receiving end.